Managed Cybersecurity and Compliance services in Los Angeles
Secure Remote Editing for Modern Post-Production Where Remote Editing Meets Enterprise-Grade IT Security.
CYBERSECURITY SOLUTION PROVIDER
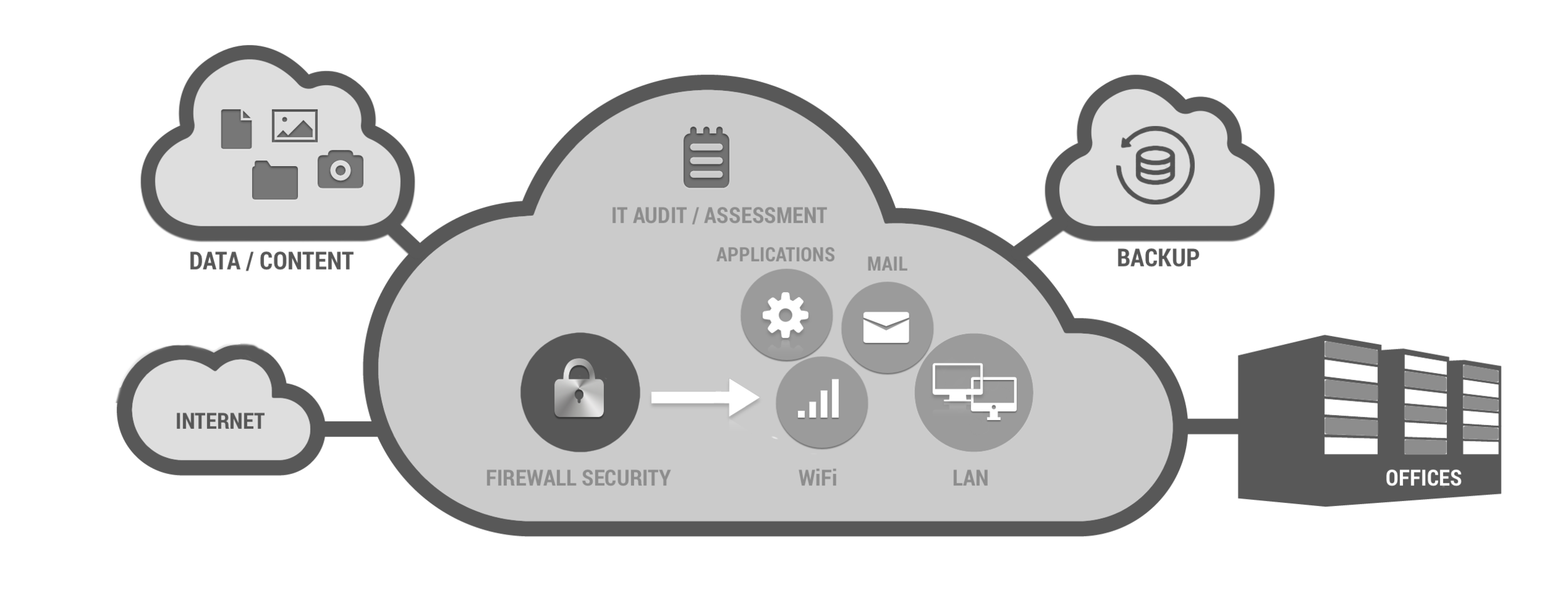
Our managed cybersecurity services covers: Audit Readiness, Risk Assessment, Network Security, Incident Response, Disaster Recovery, Business Continuity, Data Loss Protection, Endpoint Management, Security information and Event Management (SEIM), Penetration Testing, Network Vulnerability Management, Penetration Testing, Security Awareness Training, and Remediation Services.
Los Angeles–based managed IT and cybersecurity provider specializing in the media and entertainment industry. We partner with agencies, trailers, and post-production companies to streamline audit preparation by delivering comprehensive content security strategies, content protection, vulnerability assessments, security risk assessment, data loss protection, security awareness training, network security, compliance management, and penetration testing. Our solutions help safeguard sensitive data and intellectual property from cyber threats while ensuring compliance with industry regulations and content security requirements based on MPA content security best practices. Below is a list of services including description that we offer
1. Security risk assessment and management: A comprehensive risk assessment is conducted to identify potential vulnerabilities and threats to the IT infrastructure. Based on the assessment, a risk management plan is developed to mitigate the risks.
2. Network security: Network security measures are implemented to protect the IT infrastructure from unauthorized access, malware, and other cyber threats. This includes firewall setup with all required services around it such as intrusion detection and prevention systems (IDS and IPS), anti-spyware and anti-virus secure, email security services such as anti-phishing and anti-spam, and content filtering as well as Geo-IP filtering.
3. Network Vulnerability scanning & management: also commonly known as ‘vuln scan', is an automated process of proactively identifying network, operating systems, applications, and security vulnerabilities. The scanning process includes detecting and classifying system weaknesses in networks, network equipments, servers, shared storages, and computers.
4. Data loss protection: Data encryption, backup, and disaster recovery plans are implemented to protect sensitive data and ensure business continuity in case of a disaster.
5. Compliance management: Ensuring compliance with industry regulations by aligning the company’s security policies, procedures, and operations to meet required standards and minimize risks. This includes developing policies, training employees, monitoring security activities, conducting regular audits, and implementing corrective actions. Maintaining strong compliance helps prevent financial penalties, reputational damage, and operational disruptions.
6. Security awareness training: Employees receive comprehensive training on security best practices to reduce the risk of human error and strengthen the organization’s overall security posture. This training covers topics such as proper handling of sensitive data, recognizing and reporting phishing attempts, safe use of company devices, password hygiene, and adherence to access control procedures.
7. Incident response and management: A well-defined incident response plan is developed to handle security incidents and minimize their impact on the business which is essential for protecting company’s data and systems, minimizing the impact of security incidents, and ensuring compliance with legal and regulatory requirements.
My Remote Tech has worked with numerous production studios and content creators in the media and entertainment industry to ensure their data and content security is compliant with TPN (Trusted Partner Network) latest security standards, which are based on the Motion Picture Association - MPA security guidelines and best practices.
Leader in IT Security, Cybersecurity, and Content Security Compliance
We are a trusted leader in IT security, cybersecurity, IT consulting, content security, IT security audits, and compliance services, delivering specialized solutions tailored for the media and entertainment industry. Our expertise includes comprehensive content security assessments aligned with the latest best practices established by the Motion Picture Association (MPA) and maintained through the Trusted Partner Network (TPN).
The MPA Content Security Best Practices provide a global framework for protecting sensitive media assets across the production, post-production, marketing, and distribution lifecycle. These practices define the minimum security preparedness requirements for service providers handling studio content, helping organizations mitigate risks such as data breaches, piracy, leaks, and unauthorized access.
Our services are designed to help studios, production companies, marketing agencies, and post-production facilities implement robust security frameworks that meet or exceed industry standards. Through a combination of technical security controls, governance policies, and operational best practices, we help organizations secure digital assets, maintain compliance, and strengthen their overall cybersecurity posture.
Our Core Expertise
IT Security & Cybersecurity Consulting
Advanced security architecture design, threat mitigation strategies, and proactive defense against modern cyber threats.Content Security for Media & Entertainment
Protection of high-value creative assets including films, television productions, trailers, marketing materials, scripts, and digital media files.TPN / MPA Content Security Assessments
Security gap analysis and readiness assessments aligned with the MPA Content Security Best Practices and TPN security framework.IT Security Audits & Compliance
Comprehensive audits covering infrastructure, cloud environments, applications, and workflows, ensuring compliance with industry frameworks such as ISO 27001, NIST, and MPA/TPN requirements.Secure Production & Post-Production Workflows
Implementation of secure pipelines for remote production, cloud collaboration, asset transfer, and digital content management.Risk Management & Security Hardening
Identification of vulnerabilities across networks, systems, applications, and content workflows, followed by structured remediation plans.
Protecting Content Across the Entire Media Supply Chain
We help organizations implement security controls across every stage of the content lifecycle, including:
Pre-production and creative development
Production and editorial workflows
Post-production and VFX pipelines
Marketing and distribution workflows
Cloud and remote collaboration environments
Our approach ensures that sensitive media assets remain secure, traceable, and protected from unauthorized access or leaks, while enabling creative teams to collaborate efficiently.
Trusted Security Partner for the Entertainment Industry
By aligning with the latest MPA Content Security Best Practices maintained by TPN, we help organizations achieve industry-recognized security readiness, enabling them to work confidently with major studios, streaming platforms, and global content owners.
Our mission is to strengthen cybersecurity, safeguard intellectual property, and protect the integrity of digital content throughout the global media supply chain.
-
Security Risk Assessment
We offer security risk assessments to identify, estimate and prioritize risks to client’s operations and assets resulting from cyber attack.

-
Network Vulnerability Scan
We perform external and internal comprehensive network vulnerability assessment to find their external network vulnerabilities.

-
Penetration Testing
Every business MUST have a secure and safe network in order to have minimum security for protecting their assets “data” and operate.

TPN+ Security Assessment Preparation
We can assist you in a Cybersecurity audit for the media and entertainment industry based on Motion Picture Association “MPA” Content Security Best Practices maintained by Trusted Partner Network “TPN” and any remediation if needed. This will cover the assessment preparation which includes controls and security policies, Network diagram, Risk assessment, Network Vulnerability, and Penetration testing to ensure your facility meets the MPA Content Security Best Practices by TPN prior to commencing a real assessment.
NEXT GENERATION FIREWALL SERVICES AND SUPPORT
Intrusion Detection System
Intrusion Prevention System
Block security incursions
NGAV for all security threats
Traffic shaping for bandwidth management
Identity-Based Access Control
Secure VPN setup for remote users
Firewall Policy/Access Rules setup
Secure Sockets Layer (SSL) setup
Deep packet inspection (DPI)
Intelligence advance threat protection
Multi-factor authentication (MFA/2FA)
Centralize logging and monitoring
Content filtering
Email Security
Quality of Service (QoS)
Single sign-on
VLAN setup and management
SD-WAN support
Remote Monitoring
Our remote monitoring and management will ensure your IT infrastructure uptime. In fact, your network infrastructure will stay up 99.95% of times. Another great result from remote monitoring is preventing any security incidents, meaning that we will detect any possible security attack or breach or virus, malware, & ransomware before even touch the network.
Media Workflow Policy
Workflow can be simple of paper but very complex with all required unidirectional and bidirectional permissions, network access level, and firewall rules and policies when it comes to implementation. We will create a media workflow policy that is easy to implement and in compliance with TPN security requirements according to your facility type and content handling requirements.
Network Access Control
Access control policy is the foundation and base of media workflow that defines the importance of security in every media workflow policy. Our expertise will ensure your ingest and egest procedure are in compliance with the TPN based on MPAA best security practices.
Network Vulnerability Scan
Vulnerability scanning is an inspection of the potential points of exploit on a computer or network to identify security holes. As a result, we detects and classifies system weaknesses in computers and networks in order to prevent any sort of virus, malware, and hacking.
Penetration Testing
As a key component of PCI DSS, HIPAA, MPAA, and other industry standards, penetration testing attempts to gain access to the organization’s critical systems by exploiting discovered vulnerabilities. My Remote Tech simulates the attack using the same tools and intensity to test and assess the effectiveness of the security controls.
Next Generation Firewall
Looking to boost your production network’s Layer 7 protection and security with a Next-Gen Firewall? Looking for smarter and better security? Next generation firewall can protect your entire network and data with the smartest technology. We provide firewall security services that is also a main requirement for TPN and every business.
Management System
✓ Security Risk Management
✓ Security Awareness & Training
✓ Incident Response
✓ Business Continuity and Disaster Recovery
✓ Change Control Management
✓ Media Workflow
✓ Segregation of Duties
✓ Background Checks
✓ Confidentiality Agreements
✓ On-boarding/Off-boarding
Physical Security
✓ Logging and Monitoring
✓ Asset Monitoring/Management
✓ Entry / Exit Points
✓ Visitor Entry / Exit
✓ Identification
✓ Alarms
✓ System security hardening
✓ Electronic Access Control
✓ Keys
✓ Cameras
✓ Disposal Policy
Digital Security
✓ Firewall / WAN / Perimeter Security
✓ LAN / Internal Network Security
✓ Mobile Management/Security
✓ I/O Device Security
✓ Account Management
✓ Authentication/Password Policy
✓ Network Logging and Monitoring
✓ Email Security
✓ Transfer Device Methodology
✓ Internet Policy
✓ Cloud Security Policy
MPA Content Security best practices covers:
CONTENT SECURITY PRE AND POST ASSESSMENT
Trusted Partner Network (TPN) is a global, industry-wide media and entertainment content security initiative and community network, wholly owned by the Motion Picture Association, building a more secure future for content partners. TPN provides programming intended to address security in various contexts and at various points in the content pipeline. These include: the Motion Picture Advertising (MPA) Content Security Best Practices, which are maintained by TPN, and establish a single benchmark of minimum security preparedness for content owners.
Need guidance for TPN compliance or any of below services?
Content Security Program Development
Policies and Controls Development
IT Infrastructure Security Reviews
Incident Response
Disaster Recovery
Security Risk Assessment
Vulnerability Scan & Monitoring
Penetration Testing
Pre-Assessment Preparation & implementation
Post-Assessment Remediation & implementation
We ensure that your studio complies with all the security requirements set by the MPA, CDSA, and TPN.
Leader in, IT security, cybersecurity, IT consulting, Content Security, IT Security Audit and Compliance, and Content security assessment based on latest MPA content security best practices maintained by TPN serving media and entertainment industry